Have you ever heard of Business Email Compromise (BEC or Email Accounting Compromise)? At first glance, it’s a scam not unlike phishing. Accountants and bookkeepers should be particularly aware of BEC attacks for data security reasons, as required by the Federal Trade Commission.
But while phishing scams can now be easily spotted because of tell-tale red flags in phishing emails, BEC schemes rely on looking like human activity. These schemes typically get control of an email account and then request for a bank transfer or a similar transaction. They also use wording to make it seem like the request is an ‘Urgent’ one or needs to be completed ‘ASAP.’
Last year, the Internet Crime Complaint Center reported $40M in losses associated with BEC schemes. BEC schemes have been reported in all 50 states, and these numbers are expected to rise in the coming months.
As time goes on, hackers come up with more and more elaborate schemes to trick people into giving them sensitive data, and BEC is a classic example of this.
Here are the ways to secure your firm against BEC attacks:
1. Monitor anomalous behavior.
Ensure that your remote team members are accessing sensitive client data and company accounts securely.
The increase in remote work means firms rely on cloud-based services like Microsoft Office, Dropbox, and other document-sharing applications more than ever before. Make sure that there are no log-ins at out-of-office hours to these apps.
Learn more about why access management matters for accounting firms, and how Practice Protect helps CPAs manage access within their organizations.
2. Be careful of sudden email account changes.
Always verify an email address if something seems different with their domain name.
The migration process when changing a firm’s domain and email platform can leave the mail server open to breaches. If you’ve noticed that an email’s domain has changed, always request verification of an email address if you receive an email from a vendor or even someone from your own firm about a financial matter.
3. Check email addresses for even the slightest discrepancies.
Even the smallest differences in email addresses can spell disaster for your firm.
A common trick hackers use is to slightly change email addresses to make them still appear legitimate. The usual culprit is the capital letter “I” being substituted for a lowercase “L”, making them appear similar.
4. Enable Multi-factor Authentication (MFA) for email accounts.
Is MFA enabled for your company accounts?
MFA ensures that even if a hacker has access to your email credentials, they would still need access to an authentication app (usually on a mobile device). This adds an extra layer of security. It is best practice to enable MFA for your firm’s email accounts.
5. Add a banner to messages coming from or sent by team members in your organization.
Consider enabling this configuration for your email system. The banner should warn users if an email address is coming from someone outside your organization.
See our example below:
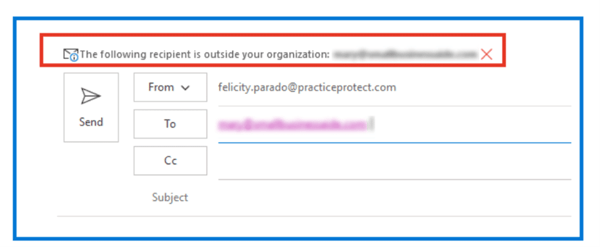
An email banner serves as your first red flag for any suspicious or unfamiliar addresses.
6. Turn on antivirus features that block malicious emails.
Double-check that important antivirus features are turned on for all devices in your firm.
Your firm might have antivirus licenses, but are the features that block suspicious emails or phishing emails enabled? Some of us might be guilty of buying an antivirus program but haven’t used it beyond running virus scans.
7. Set up a system within your firm to double-check payment requests.
Make sure all your bank transfer requests are validated by setting up a confirmation process first
A good rule of thumb when receiving payment requests or bank transfers is to check with whoever requested it to ensure this is a legitimate request.
Internally, we have a system set up where our Finance team members would always double-check with whoever requested a payment or bank transfer using a chat method. This process ensures that the team member is communicating with whoever requested the transfer using a different channel.
Securing your email systems and educating your team about best practices when it comes to email security go a long way towards BEC-proofing your firm. If you’d like to know more about Practice Protect’s email security function, schedule a time with us here.
.png?width=150&height=63&name=TWRlogo-regmark_blueblack%20(1).png)
.png)








Do you have questions about this article? Email us and let us know > info@woodard.com
Comments: